A network administrator wants to permit Telnet traffic initiated from the address book ent
ry the10net in a zone called UNTRUST to the address book entry Server in a zone called TRUST.However, the administrator does not want the server to be able to initiate any type of traffic from the TRUST zone to the UNTRUST zone.Which configuration statement would correctly accomplish this task?()
A. from-zone UNTRUST to-zone TRUST { policy DenyServer { match { source-address any; destination-address any; application any; } then { deny; } } } from-zone TRUST to-zone UNTRUST { policy AllowTelnetin { match { source-address the10net; destination-address Server; application junos-telnet; } then { permit; } } }
B. from-zone TRUST to-zone UNTRUST { policy DenyServer { match { source-address Server; destination-address any; application any; } then {deny; } } } from-zone UNTRUST to-zone TRUST { policy AllowTelnetin { match { source-address the10net; destination-address Server; application junos-telnet; } then { permit; } } }
C. from-zone UNTRUST to-zone TRUST { policy AllowTelnetin { match { source-address the10net; destination-address Server; application junos-ftp; } then { permit; } } }
D. from-zone TRUST to-zone UNTRUST { policy DenyServer { match { source-address Server; destination-address any; application any; } then { permit; } } } from-zone UNTRUST to-zone TRUST { policy AllowTelnetin { match {source-address the10net; destination-address Server; application junos-telnet; } then { permit; } } }
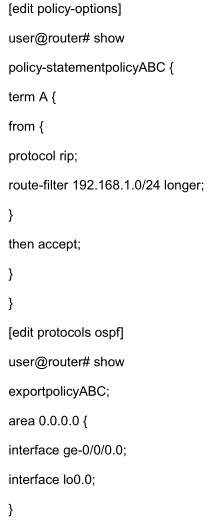
 题目内容
(请给出正确答案)
题目内容
(请给出正确答案)
 如搜索结果不匹配,请 联系老师 获取答案
如搜索结果不匹配,请 联系老师 获取答案